Trusted applications and policy settings
Posted: February 16th, 2012 | Author: Michael | Filed under: Lync Development | Tags: external access, federation, policy, provisioning, trusted application endpoint, voice policy | 3 Comments »Unless your Lync environment has a single global policy for each type of policy setting (voice policy, conferencing policy, dial plan, etc.) you may run into problems where your UCMA trusted application endpoints don’t work properly with the default policy. A couple of common examples:
- Voice policy – the default collection of PSTN usages may not be appropriate for the PSTN calls initiated by your application
- External access policy – if your application needs to contact public IM or federated users and the default policy doesn’t allow this
Normally, the Get-CsTrustedApplicationEndpoint command in Lync Management Shell doesn’t show any policy information about the trusted application endpoints, and so it’s easy to get the idea that they don’t HAVE any policies. But in reality, the policies are there — they’re just hiding.
Here’s what typical results from Get-CsTrustedApplicationEndpoint look like:
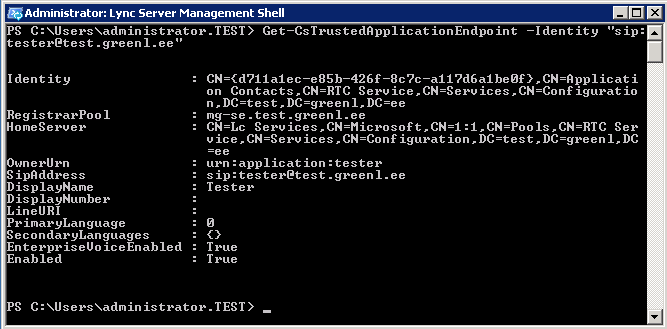
As you can see, no policy settings show up here. But that changes if you run the command like this:
Get-CsTrustedApplicationEndpoint -Identity "sip:tester@test.greenl.ee" | Select-Object *
Now, the command divulges a whole bunch of other properties that you wouldn’t have guessed were there:
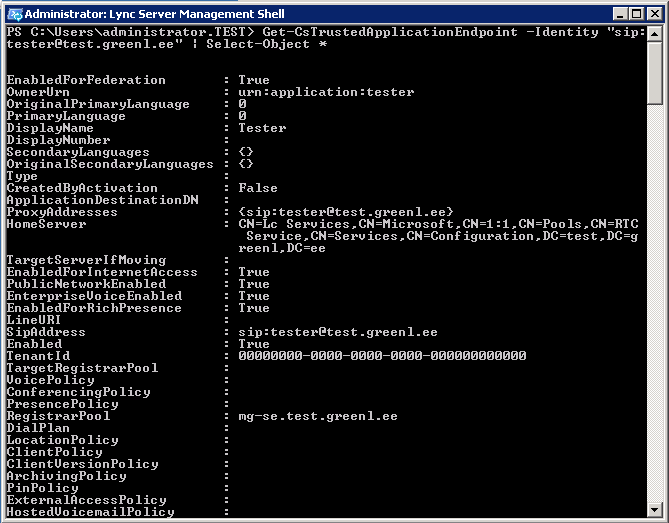
Lo and behold, all of the policy settings you can set for normal users are there as well.
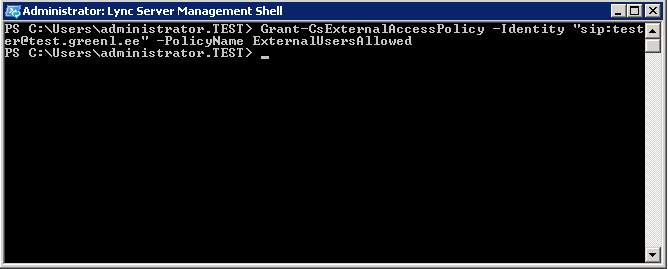
So what if we want to assign a different policy? Simple — just do it the same way you would for a normal user. Here’s an example:
Grant-CsExternalAccessPolicy -Identity "sip:tester@test.greenl.ee" -PolicyName ExternalUsersAllowed
Here’s the result:
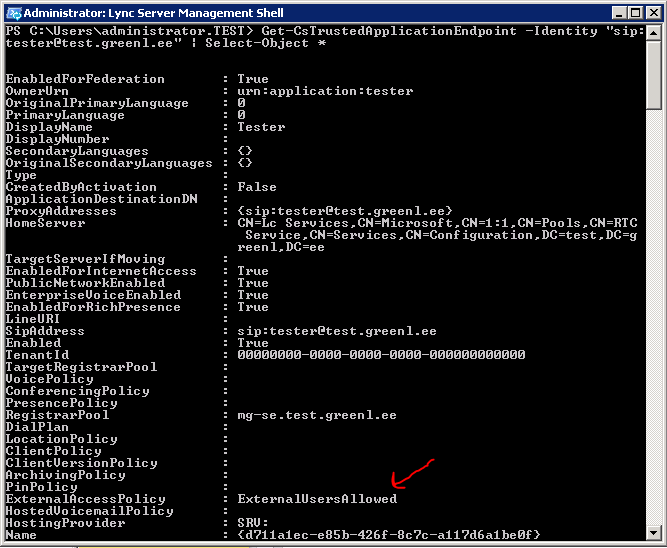
The trusted application endpoint now has the user-level policy assigned.
Have fun granting policies to your endpoints, and, as always, let me know if you have comments or questions.
Hi Michael,
we are having issues with users trying to call a TrustedApplicationEndpoint, the error in Lync Diagnostics is;
“The client is attempting to join another endpoint that has not been provisioned” component=”Audio Video Conferencing Server”.
I have checked the Voice Policy, Dial Plan etc.
The TrustedApplicationEndpoint did just have the ‘Client Authentication, Server Authentication’ (Computer Template) certificate renewed.
You just may have seen this issue before.
Regards Kim
Hi Michael,
thanks for this info, I was trying to find policy settings for my trusted application and this helped quite a bit 🙂
Glad it was helpful!